FACT for Vendors & OEMs
Continuous assurance of your software supply chain
Manage Software Component Suppliers
FACT Check your software supply chain and your releases through your development and release process — before they get into the wild.
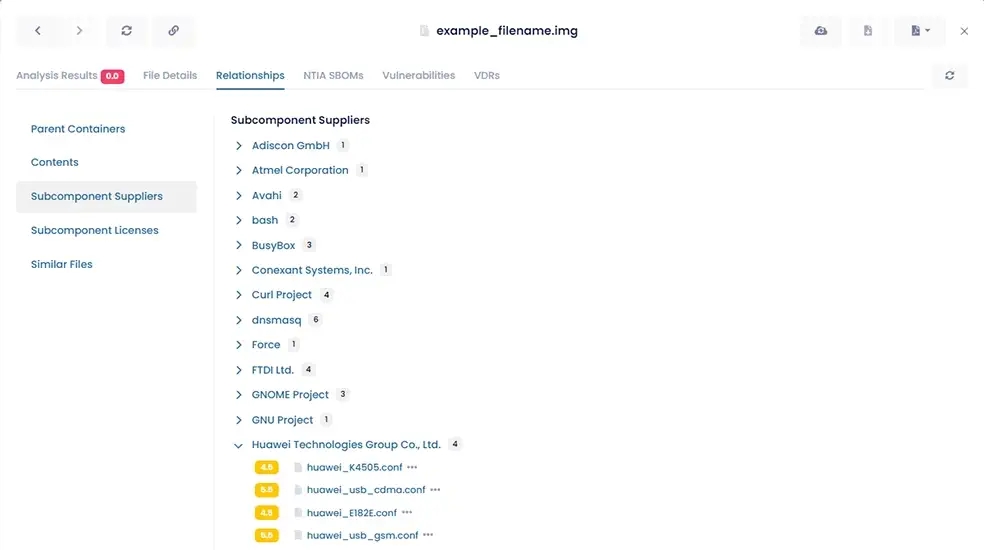
As a part of the software supply chain, you need to know the risk profile of all the 3rd, 4th... nth-party software embedded in your products. This intelligence helps you avoid dangerous suppliers, get ahead of issues before they are public, and determine risk embedded in your full software portfolio. FACT can help, offering:
- Interactive SBOMs for fast component impact analysis
- Risk and reputation intelligence on all components
- Component traceability across product lines and lifecycle
- Advance notice of pending malware or vulnerability reports
Do you know the security profile of your 3rd-party software suppliers?
Automate Compliance
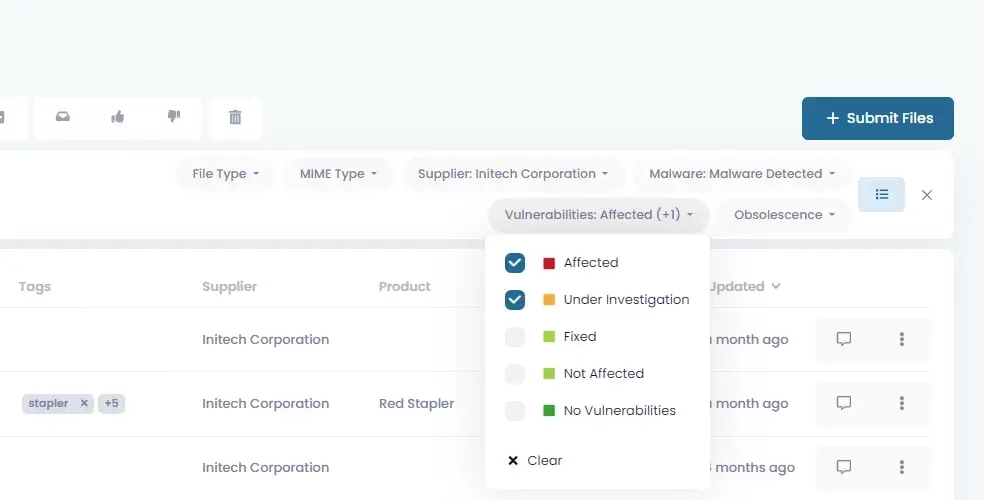
Securing your development environment means knowing which components are showing up in vulnerability databases, as well as where and when you’ve used them.
It also means protecting your code-signing certificates and ensuring the software you post is exactly what you intended to go to your customers. FACT can help, offering:
- Risk intelligence on the origins of all components
- Traceability for all components in all released packages
- AI-driven vulnerability suggestions you control
- Support across multiple O/S and packages
- Visibility and control
Are you still addressing compliance and 3rd-party governance manually?
Improve Support and Distribution
Track-and-trace your software product releases through your distribution chain to ensure they don’t get into the wrong hands.
To protect your customers and your reputation, you need to know which customers were shipped packages with vulnerable components and understand any cybersecurity warnings these might generate in your customers’ operations. You need to provide vulnerability and obsolescence updates and help customers meet regulatory requirements. FACT can help with:
- Clear vulnerability reporting, including SBOMs and VEX document support
- API support for your cybersecurity service teams
- Detection of customer false positives
- Branded tools for customer package validation
Do you know where your software went?
Let's get in touch so we can show you what FACT can do for OEM/vendors.
FACT Platform Features
Benefits
SBOMs
- 1-click NTIA-compliant SBOMs in SPDX JSON and SPDX Tag/Value formats
- Enriched SBOMs offering drill down-and-around to expose vulnerable components across your portfolio
- VEX (Vulnerability Exploitability eXchange) documents
- Build brand loyalty through transparency
- Create and maintain a competitive advantage
- Increase product quality
- Provide audit evidence for regulations
- Help customers focus on exploitable vulnerabilities
Continuous Supply Chain Visibility
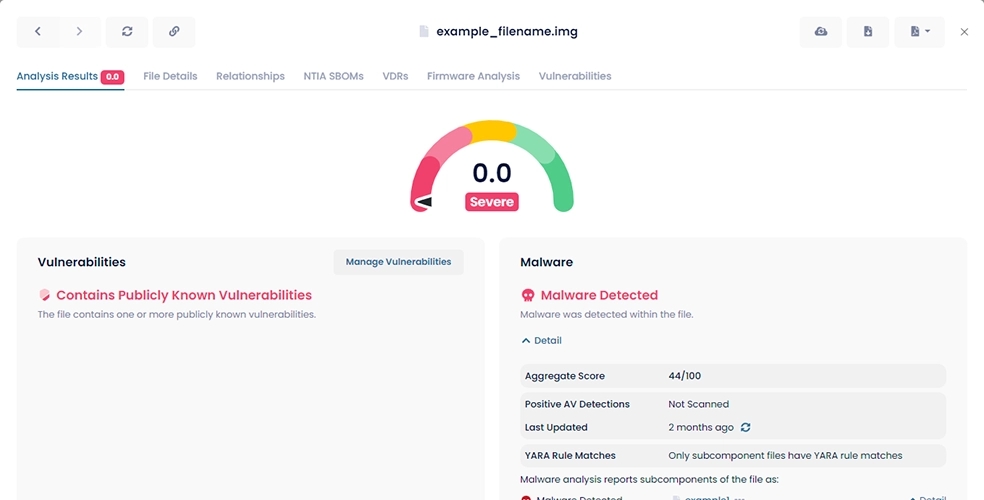
- Software validation and easy-to-use scoring
- Malware detection via multiple AV sources and over 18,000 YARA rules
- Certificate chain and signature validation
- In-the-wild monitoring for unauthorized or fraudulent files
- Release and update artifact tracking
- Gain detailed visibility into all the vendors, products, and components in your portfolio
- Gain operational insights
- Reduce time spent on malware false positive reports
- Manage software obsolescence
- Reduce operational costs through automation
Vulnerability Management
- AI-driven scanning of public resources
- Natural language processing to overcome inconsistent naming
- Vulnerability suggestions where suspected
- Get in front of high-profile vulnerability announcements
- Find vulnerabilities in all products in minutes, not days
- Reduce costs through automated vulnerability research
Risk and Compliance Management
- 3rd-party supplier discovery
- Supplier quality assessments
- Risk profiles in product line/portfolio
- Detection of high-risk software and components
- Executive reporting and KPIs
- Protect your brand and reduce potential liability
- Make informed procurement decisions
- Drive governance and audit of SDLC policies
- Be prepared for M&A due diligence
Scalability, Security, Performance
- Full-featured RESTful API
- Cloud (SaaS) platform with portal
- Vendor-, platform-, and operating system-agnostic
- 11 billion analysis operations/day
- 1.4 billion mapped relationships between parent-child files
- Integrate with corporate systems, workflows, and processes
- Be assured thanks to proven AWS security best practices
- Address IT, IoT, and OT products with a single solution
- Consolidate visibility for PSIRTs and product management
aDolus FACT Supply Chain Assurance
Manage Software
Supplier Risk
- Supplier Risk Management
- Compliance and Audit
- Reputation Management
- Legal/M&A
Manage Development & Deployment Risk
- Development & Deployment Risk Management
- Product Management
- Quality Assurance
- Configuration Management
Manage Support Ops & Distribution Chain Risk
- Risk Management
- Incident Response
- Customer Support
- Field Operations
- Digital Business Operations
- Cybersecurity Service Teams